Mexico’s Mobile Phone Registry and the Myth of Security
The man in front of you at the OXXO counter is holding his phone and his INE.
The clerk squints at the screen. The system freezes. Someone sighs.
A form asks for a CURP, a photo, confirmation of identity—again.
Outside, extortion calls continue uninterrupted.
This is how it begins. Not with a speech. Not with a law journal.
With a shrug.
There is a recurring fantasy inside modern states: the idea that society can be fixed if only it becomes legible.
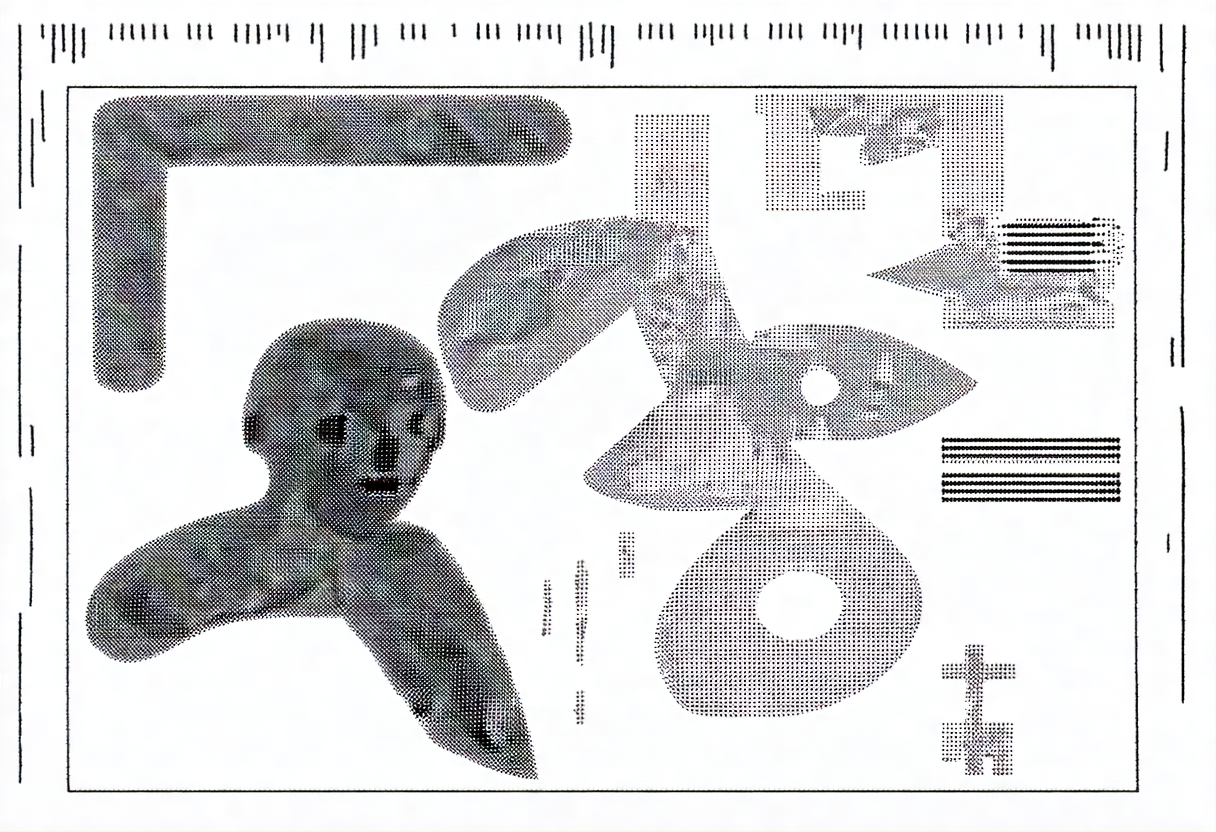
Not understood, protected or represented. Just readable. A barcode civilization.
And so, almost inevitably, we return to one of the state’s oldest addictions: the registry. The padron. The sacred list. The belief that if every human is tied to an ID, a number, a face, a CURP, a biometric marker, then crime will shrink, chaos will retreat, and order will re-emerge.
But here’s the uncomfortable truth: registries do not fight crime. They fight anonymity. And anonymity is not a crime. It is, in many cases, the last remaining form of civic shelter.
1) The New Ritual (and Old Romance): “Register Your Line”
The official premise is familiar: linking every phone line to a verified identity will reduce fraud, extortion, and anonymous threats. Remove anonymity, remove crime.
This is not Mexico’s first registry romance.
Early Attempts: RENAUT (2009–2012)
Long before 2026, Mexico tried a mandatory cellphone registry.
- In 2009, the government introduced the Registro Nacional de Usuarios de Telefonía Móvil (RENAUT). The idea was to require all mobile users to register their personal details, including fingerprints, with the registry when activating a SIM card.
- The goal was to combat extortion and kidnapping carried out via cellphones — which were increasingly used inside prisons and by criminal groups for threats and coercion.
- However, the system was ineffective and poorly implemented. Less than half of all lines were registered by 2010, and there were reports that data was leaked online and even sold on the internet.
- Because of these problems, the Senate abolished the registry in 2011 and the collected database was destroyed in 2012.
This took place nationally, under the government of President Felipe Calderón (2006–2012), and was pushed by the telecommunications regulator of the time (COFETEL, predecessor to today’s CRT/IFT system).
Main reasons behind the failure:
- Low compliance and false information
- Data leaks and security issues
- Ongoing extortion despite the registry
PANAUT (2021–2022): Biometric Revival and Supreme Court Rejection
After the RENAUT debacle, the idea lay dormant for nearly a decade — until it was revived in a different form:
- In April 2021, lawmakers passed the legal framework for the Padrón Nacional de Usuarios de Telefonía Móvil (PANAUT). Unlike the earlier registry, this required biometric data (fingerprints, facial data), CURP, address, and more.
- The justification was similar: reduce anonymous use of cellphones in crimes.
- But in April 2022, the Supreme Court of Justice of the Nation (SCJN) declared the PANAUT unconstitutional, mainly on privacy and proportionality grounds. It held that such a registry violated rights to privacy and was not justified by evidence showing its effectiveness against organized crime.
- The reform passed both chambers of Congress with broad support before judicial rejection.
- Critics included digital rights organizations and privacy advocates, who argued it was excessive and risky.
The biometric-focused registry was struck down and never fully implemented.
2026 Rollout: Registration “Without Biometrics”
And now, in 2026, it returns—leaner, quieter, more careful under a familiar costume with technical differences: public safety. Authorities insist that linking every phone line to a verified identity will reduce extortion, fraud, and threats made from anonymous numbers. The logic is seductively simple: If criminals hide behind anonymity, remove anonymity.
A neat syllogism. A bureaucrat’s dream. A spreadsheet’s lullaby. But reality is not a syllogism. Reality is a system. No longer just a list. Now a node.
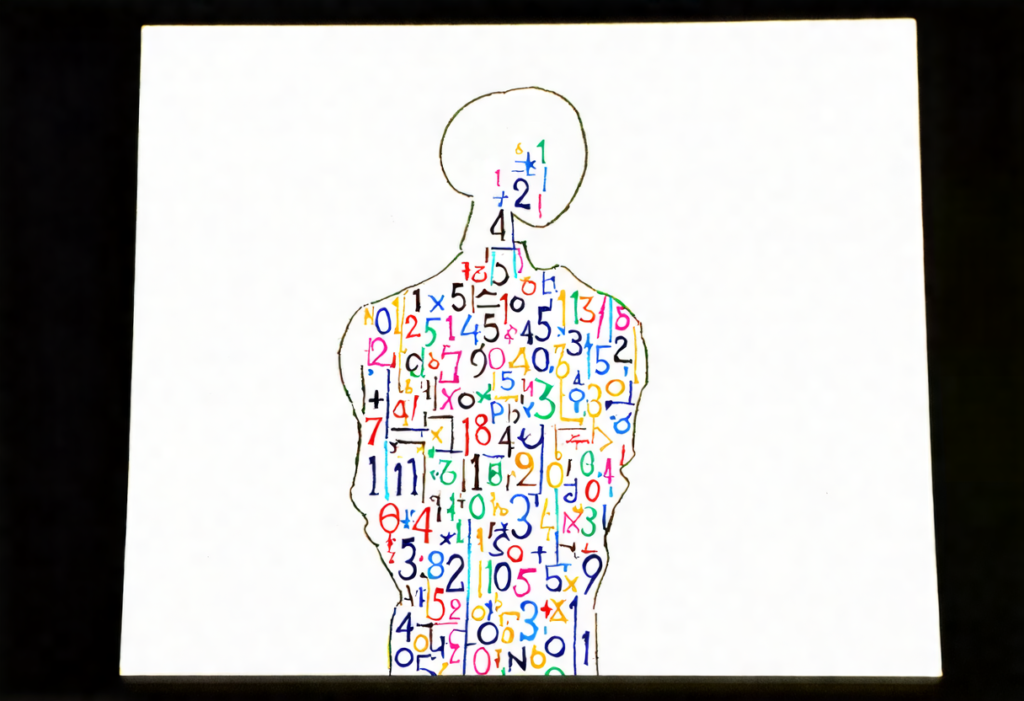
The SIM is no longer merely tied to a name; it is tethered to the biometric CURP—a persistent identity spine that links your phone, your body, your documents, your digital voice.
This time, the state is not just asking who you are.
It is anchoring who speaks to who exists.
And Mexico is not a laboratory country where institutions are reliable, police do their job, prosecutors prosecute, judges judge, and data is protected. Mexico is a country where the state is often weak where it must be strong and strong where it should be humble.
So what the registry really becomes is not a crime policy.
It becomes something deeper:
A declaration that the citizen is guilty until indexed.
SYSTEMIC EXPOSURE POINT #1
The state tends to govern what it can count, not what it can actually solve.
Crime is hard. Corruption is lethal. Impunity is structural.
But paperwork? Paperwork is easy.
The state does not abandon failed ideas; it refines them until resistance becomes impractical.
2) Soft Authoritarianism Wears a UI: “For Your Own Good”
The interesting thing about modern authoritarianism is that it rarely wears boots.
It wears terms and conditions.
It doesn’t usually arrive with tanks. It arrives with:
- compliance deadlines
- platform portals
- technical requirements
- “just verify your identity”
- “it’s free”
- “it’s quick”
“it’s mandatory”
And then comes the coercion — gentle, administrative, polite:
Don’t register? Your line gets suspended.
No ideology required. No propaganda posters. No censorship squads. Just infrastructure.
This is what I call authoritarianism by design: you are free to resist, but your resistance is punished through the removal of basic participation in modern life.
No phone line means no:
- business communication
- banks and 2FA messages
- rides
- deliveries
- emergencies
- work coordination
- Airbnb, MercadoLibre or Uber operations (as client or work)
- even basic family logistics: No calls from your child’s school when they get sick.
The registry is not violence.
It is dependency weaponized.
SYSTEMIC EXPOSURE POINT #2
When the state cannot guarantee protection, it starts demanding obedience instead.
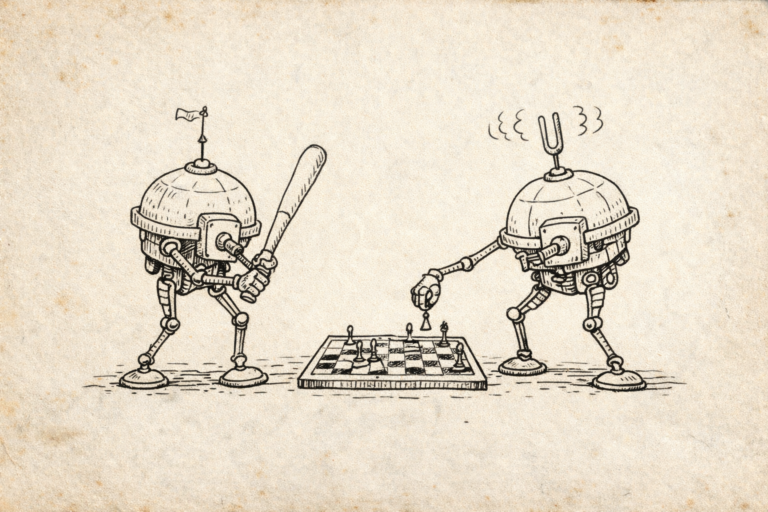
3) The Fiction of the “Identified Criminal”
Here comes the inevitable counterargument:
“But legitimate law enforcement needs tools. If you’re not doing anything wrong, why worry?”
Because this assumes crime operates the way policy memos imagine it does.
The registry presumes that criminal activity depends on anonymity. This is the part that exposes the state’s detachment from how crime actually functions in Mexico.
Serious crime does not operate as:
“unknown person buys SIM and commits crimes from it”
Serious crime operates as:
- coercion
- recruitment
- stolen identities
- forced registrations
- bribed clerks
- internal accomplices
- corrupted enforcement
- protected networks
If a cartel needs phone lines, it will not be stopped by CURP requirements. It will simply procure them using:
- purchased identities
- dead identities
- bribed systems
- front people
- intimidation
A registry doesn’t eliminate the resource. It changes the market.
So what happens next is predictable:
a black market of registered lines emerges.
The state then declares war on the black market it just created.
And the cycle continues: new laws, more surveillance, more compliance rituals — with the same outcomes.
SYSTEMIC EXPOSURE POINT #3
When policy does not address root incentives, it becomes a loop:
problem → symbolic solution → adaptation → bigger problem → stronger symbolic solution.
4) “But It’s Not Government-Controlled”: The Private State
A favorite rhetorical escape route is:
“It’s not a centralized government database. The companies hold the data.”
As if that makes it safe; is not reassuring.
On January 9, 2026—less than 24 hours after launch—the Telcel portal exposed sensitive user data without authentication. Names, CURPs, RFCs. Publicly documented. Quietly fixed after exposure.
This is not a glitch.
This is the model.
The state is building a vault with one key,
then handing copies of that key to every telecom clerk, contractor, and backend system in the country.
Private companies collect identity data at national scale.
Hackers attack it.
Criminals buy it.
Insiders leak it.
Authorities request it.
Citizens absorb the risk.
This is how modern governance works now: the state does not need to control the database directly — it only needs the power to demand access.
So we get the most fragile possible arrangement:
- private companies collect sensitive identity data at massive scale
- hackers attempt to exploit it
- criminals attempt to buy it
- insiders attempt to leak it
- government agencies attempt to access it
- citizens attempt to survive it
This is a surveillance ecosystem disguised as “consumer registration.”
In a country with deep corruption, weak accountability, and a long history of leaks, forcing mass aggregation of sensitive data is not a security policy.
It is a security vulnerability factory.
SYSTEMIC EXPOSURE POINT #4
The state is outsourcing risk to the population:
if the database leaks, it’s not the authorities who suffer—
it’s ordinary people.
5) The Friction Tax and Digital Eviction and Privacy as Luxury Product
Here’s the most cynical part of the whole story:
Mexico has privacy laws.
Mexico has regulatory language.
Mexico has theoretical frameworks.
But what good is a right that cannot be defended?
Rights that depend on expensive legal machinery are not rights.
They are premium subscriptions.
So when the state says:
“Don’t worry, your data is protected by law”
The citizen hears:
“Don’t worry, you may sue—if you can afford it.”
This is where the registry becomes morally unbearable: it compels the poor and middle class into exposure, while the privileged can purchase protective layers.
- better phones
- better security tools
- legal representation
- corporate accounts
- buffers and intermediaries
- private cybersecurity
- influence networks
Privacy becomes class-coded.
SYSTEMIC EXPOSURE POINT #5
In unequal societies, “legal protection” often means:
protection exists, but not for you.
6) State Presence: Selective, Performative, and Asymmetric
The registry reveals something extremely Mexican (and tragically universal):
The state is not absent.
The state is selective.
It is present in the domains where:
- obedience can be demanded
- compliance can be measured
- penalties can be automated
- citizens have no leverage
And it is weak, hesitant, invisible, or compromised in the domains where:
- violence requires confrontation
- institutions require integrity
- officials require courage
- corruption must be purged
- impunity must be punished
So we get the inverse state:
Strong enough to demand your ID for a SIM card.
Not strong enough to dismantle extortion structures.
That is not even bad governance. It starts looking like evil.
7) The Registry as a Psychological Technology
The registry is not just a database.
It is a message.
It tells the citizen:
“We don’t trust you.
We can’t stop criminals.
But we can make you easier to track.”
And perhaps that is the true function: not security, but conditioning.
Training a population to accept that identity verification is the natural tax of existence. That you must prove you are you, at all times, everywhere, to participate in society.
This is not a war on crime.
It is a war on opacity.
And opacity is the one thing citizens must preserve when institutions cannot be trusted.
Conclusion: Legibility Is Not Safety
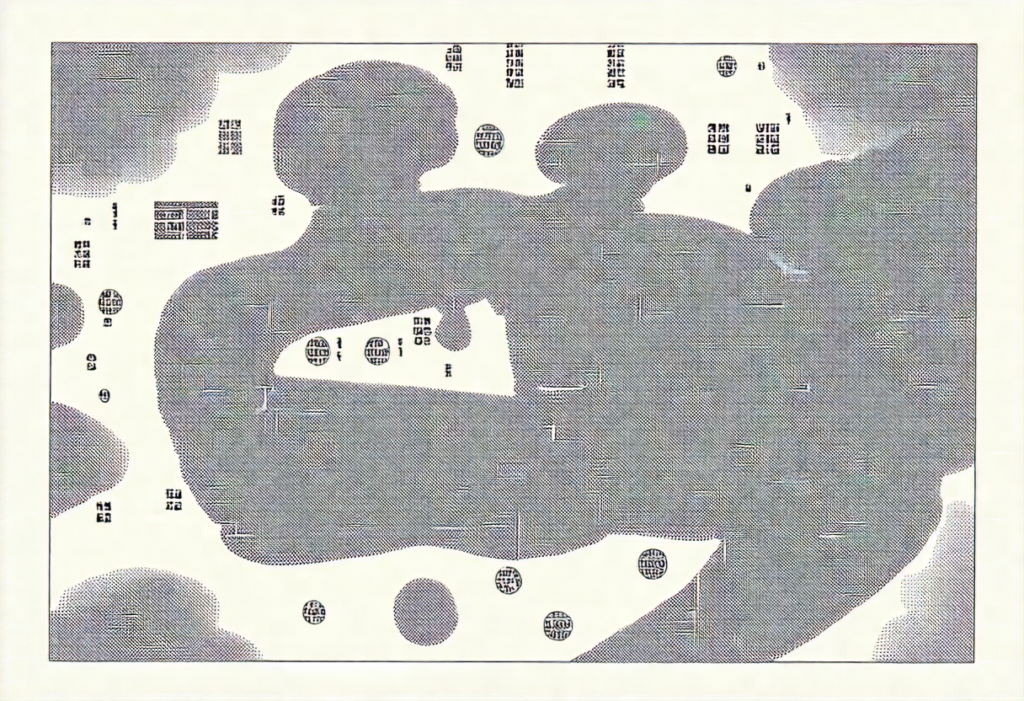
A legible society is not necessarily a safe society.
It is a society that can be sorted, flagged, paused, throttled, suspended.
Mexico’s mobile phone registry is not about crime.
It is about making the citizen readable in a system that cannot—or will not—protect them.
It may be:
- more controllable
- more taxable
- more monitorable
- more punishable
- more predictable
But safety is not produced by legibility.
Safety is produced by functioning justice, institutional credibility, low corruption, real enforcement, and real accountability.
The state cannot secure justice.
But it can always demand visibility.
And so the barcode grows longer.
The scanner more sensitive.
The silence more expensive.
The question is no longer whether this works.
The question is:
How much of yourself are you willing to surrender to a system that cannot even protect its own launch portal?
Mexico’s mobile phone registry exposes the underlying architecture of the modern state:
It cannot truly protect you,
but it can always demand visibility from you.
And that is the core danger.
Not that the registry exists.
But that it expands in the only direction in which the state consistently grows: toward citizens.